Have you ever wondered how do websites store passwords?
Why can't a Facebook or a Google employee copy your password and regain access to your account? Or why some websites tell you to set a new password, instead of sending you your forgotten password whenever you click ‘Forgot your password?’.
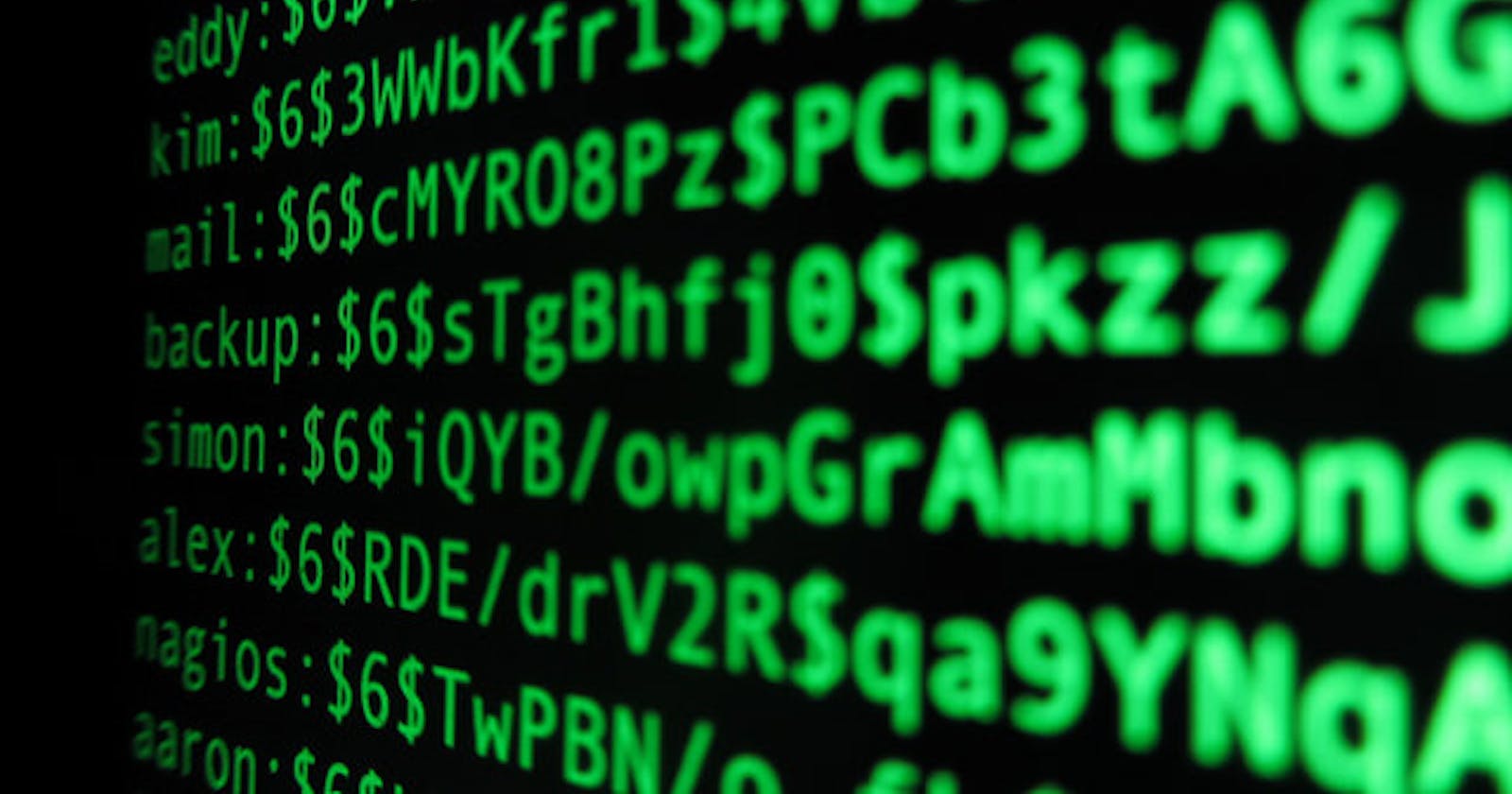
It’s because most websites nowadays don’t save passwords in plain text, instead save its algorithmic computed hash. Whenever you log in with a password, it is hashed and then compare the resultant hash with the one in the database. That means any attacker that gets to their database will only see the hash of your password, not the real one.
Rule-of-thumb: if you forget your password and the website sends it back to you in plain text, then that's how they store it. You should make sure you're not using that password anywhere else and also never to use that site again.
But what is a hash?
A hash is the output of a one-way function that takes an input and maps it to a fixed-length string that works as a unique signature for the given input and is ideally never produced with any other input (Wikepedia). The important properties of a hash function are that it is -
- Deterministic (same input gives the same hash every time)
- Practically impossible to generate the same hash from two different inputs
- It is impossible to get the input from the hash unless you try every possible input.
- Any change to the input, however small, would make the resulting hash unrecognizable from the original input’s hash. Examples of a hash function include MD5 (broken), SHA-1 (not recommended) and SHA-3 (recommended standard).
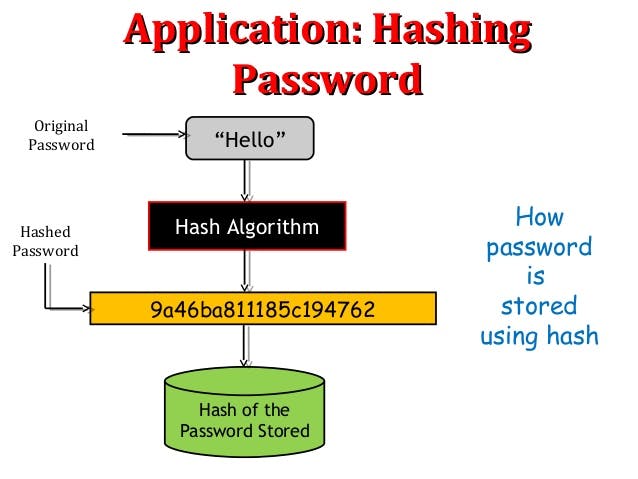
During verification -
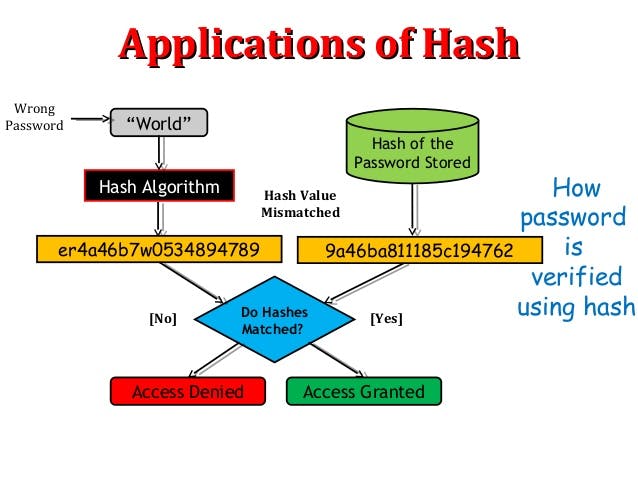
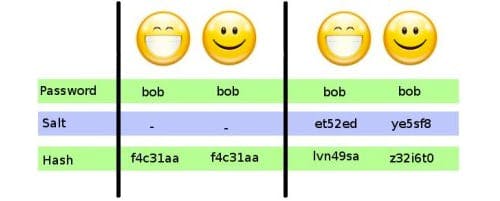
Unfortunately, many people can use the same passwords, and because hash functions are deterministic, it means that the hashes of those passwords would be the same. That means if a passwords database were compromised, and you know the password of one user, you could also gain access to whoever has the same password (because the hashes are the same).
Enter salts
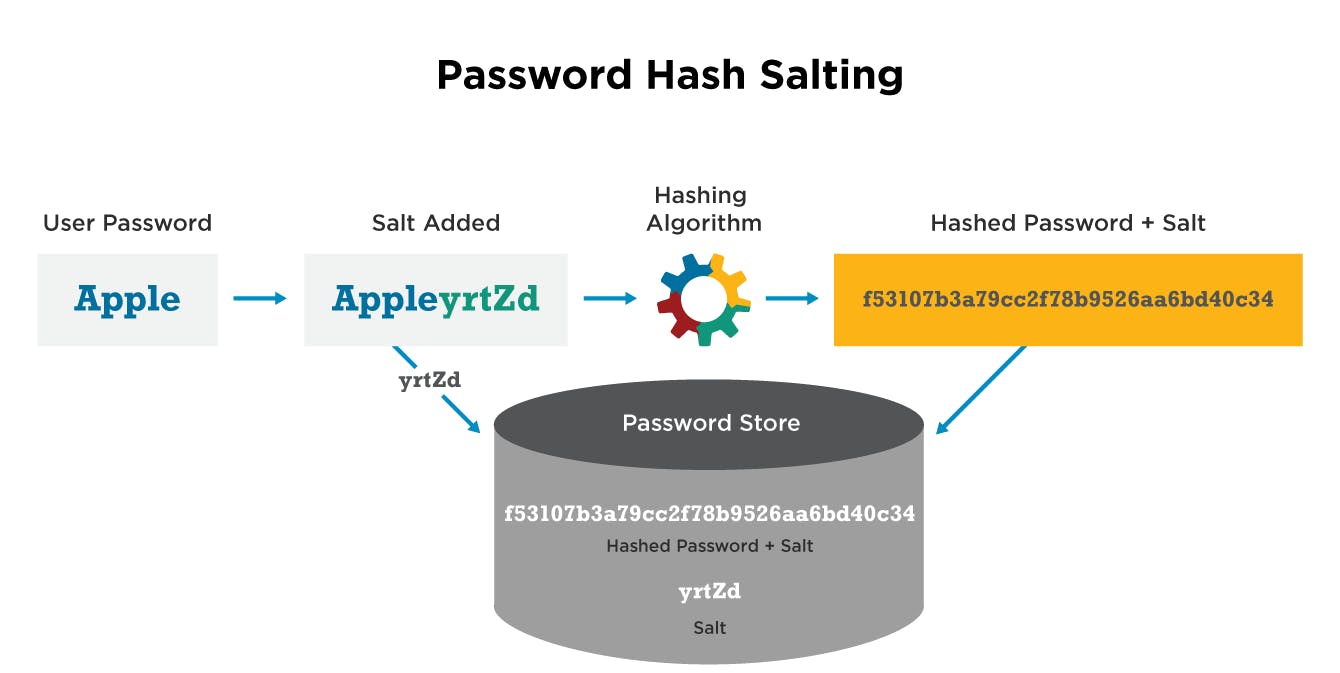
Salts are random data that are unique to each user, which are added to the user’s password before hashing it. Because of the 4th property of a good hash, the new hash is unrecognizable from the old one, thus even if user X and Y use the same password because X and Y have different, unique salts, the hash of each user’s password would look completely different. A salt can be publicly stored in plain text, as it’s just random data that doesn’t provide any insight on the user’s password.
Below image will help in understanding further -
In simpler terms -
Pass it on and help others learn if you have too. Thanks.
This was sourced from this original post. If you are a developer and further interested in securing passwords, this thread on stack exchange is for you to further read.